QuickSecure
Autonome Endpunkterkennung & Eindämmung
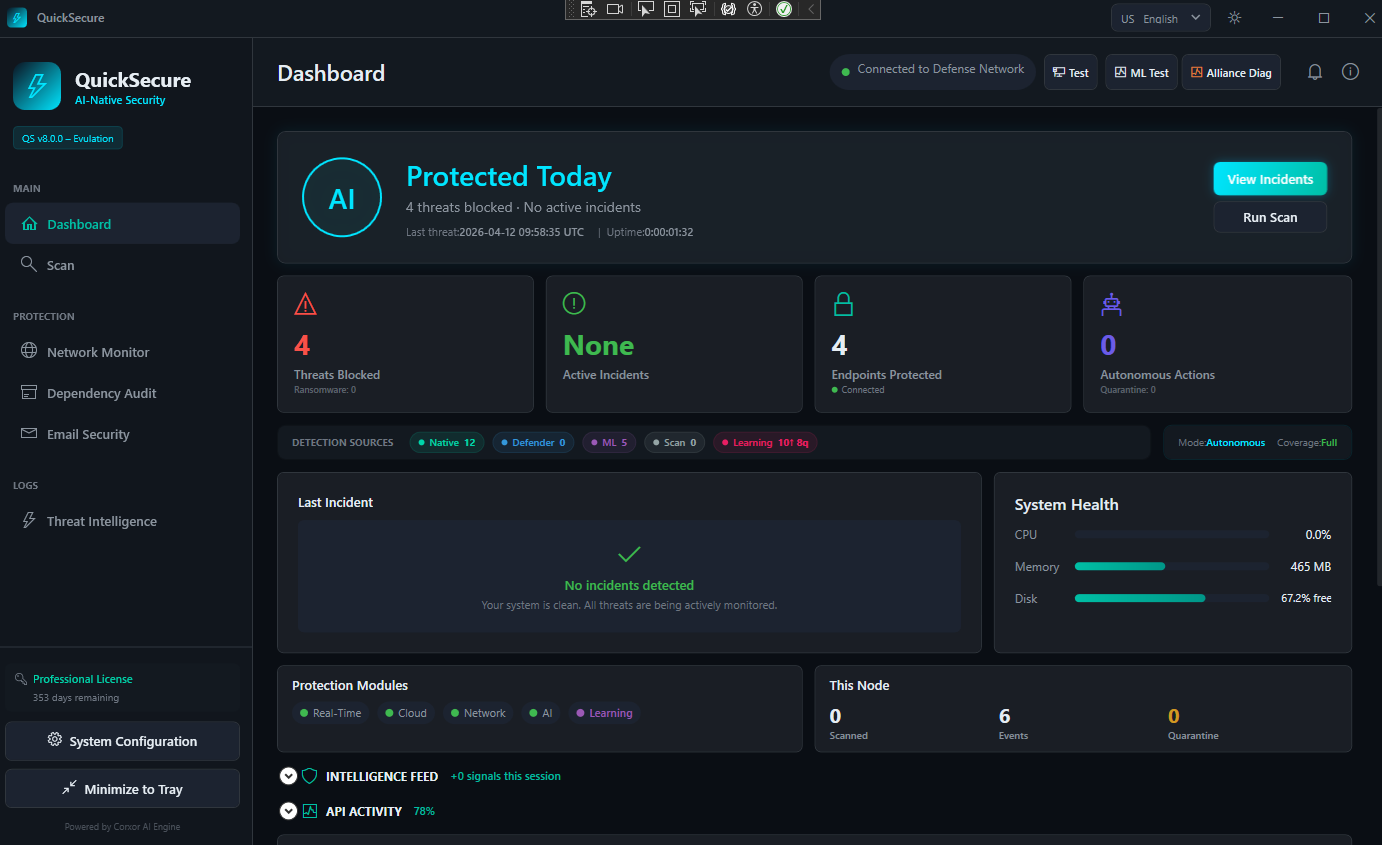
QuickSecure läuft als leichtgewichtige native Anwendung auf jedem Endpunkt. Echtzeit-Bedrohungsüberwachung, ML-gestützte Erkennung, Netzwerkverteidigung, Abhängigkeitsüberprüfung und E-Mail-Sicherheit — alles über ein einziges Dashboard mit autonomer Eindämmung.
KI-native Schutzlösung auf Ihrem Endpunkt
QuickSecure läuft als leichtgewichtige native Anwendung auf jedem Endpunkt. Echtzeit-Bedrohungsüberwachung, ML-gestützte Erkennung, Netzwerkverteidigung, Abhängigkeitsüberprüfung und E-Mail-Sicherheit — alles über ein einziges Dashboard mit autonomer Eindämmung.
Selbstlernende EDR. Cloudverwaltet. Kein Kernel-Risiko.
Ein leichtgewichtiger Agent überwacht Verhaltenstelemetrie auf Desktop- und Mobilplattformen. Versionierte ONNX-Modelle laufen direkt auf dem Endpunkt — mit Risikobewertungen, Konfidenzniveaus und erklärbaren Aufschlüsselungen.
Edge-First-Inferenz
ONNX-Modelle laufen lokal auf dem Endpunkt. Erkennungslatenz unter 15 ms. Kein Cloud-Roundtrip für Eindämmungsentscheidungen. Dreistufiges Fallback garantiert keine blinden Flecken.
Keine Kernel-Treiber
ETW und eBPF im Benutzermodus bieten tiefe Prozess-, Netzwerk- und Registrierungstransparenz ohne BSOD-Risiko. Keine Kernel-Angriffsfläche.
Cloudverwaltetes SaaS
Derselbe Agent, dieselbe ML-Engine, dieselbe Konsole für jeden Kunden. Ein neuer Mandant ist ein Datenbankeintrag — kein Infrastrukturprojekt.
Erklärbare KI
Jede Entscheidung enthält einen zusammengesetzten Risikoscore, eine Aufschlüsselung der Merkmalsbeiträge, die Modellversion und das Konfidenzniveau. Keine Blackbox-Urteile.
Multiplattform
Native Agenten für Windows, Linux, macOS, Android und iOS. Einheitliche Erkennungslogik auf allen Plattformen. Unter 80 MB Arbeitsspeicher, unter 2 % CPU.
Kollektive Verteidigung
Erkennt ein Endpunkt eine neue Bedrohung, wird die gesamte Flotte innerhalb von Minuten aktualisiert. Jeder Endpunkt stärkt den Schutz für alle.
Grundprinzip: 10 Endpunkte oder 10.000 Endpunkte — dieselbe Produktbasis. Jedes Modell-Update wird per Canary validiert. Jedes Deployment wird überwacht. Die Plattform verbessert sich kontinuierlich.
Zentrale Intelligenz, verteilte Durchsetzung
QuickSecure ist nicht nur ein Agent auf Endpunkten. Im Zentrum steht eine cloudnative KI-Sicherheitsengine, die kontinuierlich aus flottenweiter Telemetrie lernt.
Dies bildet ein kollektives Verteidigungsnetzwerk: Erkennt ein Endpunkt ein neues Bedrohungsmuster, wird die gesamte Flotte innerhalb von Minuten aktualisiert.
Null Kernel-Angriffsflaeche
ETW und eBPF im Benutzermodus bieten tiefe Prozess-, Netzwerk- und Registrierungstransparenz ohne BSOD-Risiko. Keine Kernel-Angriffsfläche.
Versionierte Modellregistrierung
Every ONNX model is versioned, signed, and tracked. Full lineage from training data to production deployment. Rollback to any previous version in seconds.
Explainable Decision Logic
Composite risk score with per-feature contribution breakdown. Model version, policy threshold, and confidence level recorded per decision. No black-box verdicts.
Drift Monitoring (PSI)
Population Stability Index tracks distribution shift between training and production features. Automatic retraining triggers when PSI exceeds configurable thresholds.
Canary Deployment
New model versions are validated on a subset of endpoints before fleet-wide promotion. Canary traffic percentage and rollback criteria are policy-defined.
Three-Stage Fallback
ONNX edge model → Random Forest → rule-based heuristics. If the primary model fails or confidence is insufficient, fallback stages engage automatically.
Embedded AI Intelligence — Not a Chatbot
The AI Security Engine is not a conversational assistant bolted onto a dashboard. It is embedded directly into security workflows — incident triage, IOC investigation, posture assessment, and operational guidance. Every AI output is grounded in your actual telemetry, structured for analyst consumption, and recorded in a tamper-evident audit log.
AI Incident Explanation
Root cause analysis, MITRE ATT&CK correlation, severity assessment, and remediation guidance — generated from structured incident data, not free-form prompts.
AI IOC Assessment
Threat intelligence correlation, confidence scoring, and contextual analysis for Indicators of Compromise — integrated directly into the IOC database workflow.
Workspace AI Assistant
Security posture analysis, threat summaries, and prioritized recommendations for your tenant — grounded in your own endpoint fleet data and threat history.
How It Works — From Agent to Control Plane
QuickSecure operates across six coordinated layers. Each layer has defined responsibilities, clear boundaries, and independent failure domains.
Endpoint Agent
Collects behavioral telemetry across 150+ forensic checkpoints on desktop and mobile. ONNX inference runs locally. Decisions evaluated against policy thresholds and operating mode constraints.
Detection Pipeline
Three-stage fallback: ONNX → Random Forest → heuristics. Every decision produces composite risk score, model confidence, and explainable feature contributions. Containment is never blind.
Control Plane & SIEM
Governs tenant isolation, policy assignment, and event routing. CentralOnly, DirectOnly, or Hybrid modes. Webhook, Syslog (CEF), and Microsoft Sentinel with transactional outbox delivery.
Central AI Engine
Aggregates fleet-wide intelligence. Model governance — registry, signing, canary deployment, drift monitoring (PSI), rollback. Distributes IoCs for collective defense.
Multi-Tenant by Design, Not by Retrofit
The default deployment model is cloud-managed SaaS. The architecture uses strict multi-tenant data partitioning, horizontal scaling of control plane components, centralized model governance, and shared infrastructure with isolated tenant contexts. There is zero per-customer code divergence.
🔒 Tenant Isolation
Each tenant gets dedicated data partitions, per-tenant ML model governance, per-tenant SIEM routing, and isolated policy contexts — all on shared infrastructure.
📈 Horizontal Scaling
Control plane components scale independently. Adding customers scales linearly — no re-architecture, no dedicated infrastructure per tenant unless explicitly requested.
🚫 Zero Custom Code
No per-customer forks, branches, or custom builds. Configuration-driven differentiation only. Consistent quality, faster updates, and lower operational cost.
Why this matters: Many security vendors position themselves as "cloud-native" while requiring per-customer deployment engineering. QuickSecure's tenant onboarding is a database record and a policy assignment — not an infrastructure project.
Progressive Trust — Earned, Not Assumed
The agent monitors over 150 forensic checkpoints covering persistence analysis (WMI, COM hijacking, registry, scheduled tasks, systemd/cron), behavioral detection (process hollowing, LSASS access, credential dumping, LOLBins, fileless malware), network intelligence (C2 beacons, DNS tunneling, AbuseIPDB/URLHaus/MalwareBazaar integration), and supply chain defense (git scanning, CI/CD integrity, typosquatting, secret exposure).
Organizations progress through three operating modes as confidence in detection accuracy grows:
Observe Only
Full inference pipeline runs, zero containment actions taken. Compares "would-contain" vs "actually-contain" to validate model accuracy before enabling autonomous behavior.
Human-in-the-Loop
Detections generate recommended actions. An admin reviews, approves, or dismisses each one. Every decision enriches the TP/FP labeling system for model retraining.
Confidence-Gated
When confidence exceeds policy threshold and risk criteria are met, containment executes automatically. Every action is logged, reversible, and feeds back into the learning loop.
Built to Survive Hostile Environments
An endpoint security product that crashes under load, loses events during outages, or allows tampering of its decision logs is worse than no product at all.
Self-Healing
Automatic recovery under degradation. The agent restores state without manual intervention when services are lost.
Backpressure
Adaptive circuit breakers prevent telemetry overload from freezing containment decisions.
Tamper-Evident
Cryptographic integrity on every event, decision, and config change. Unauthorized modifications are flagged.
ML Integrity
Model poisoning protection via signatures, drift monitoring, and canary validation.
No Vendor Lock-in
Deployable on-premise, hybrid, or multi-cloud. Architecturally independent from any single provider.
SaaS Default — Sovereign Optional
The primary deployment model is cloud-managed SaaS — fastest path to protection, first to receive updates. For regulated or sovereign environments, QuickSecure also operates in dedicated single-tenant infrastructure, on-premise data centers, sovereign cloud environments, and hybrid configurations.
The product core does not change across deployment models. The detection engine, inference pipeline, ML governance, and containment logic remain identical. Infrastructure ownership and data residency change. The security product does not.
Product vs. Service Layer
QuickSecure is the product. It includes its own SOC console — incident review, risk scoring, model confidence visualization, audit trails, policy management, and fleet intelligence — without external tooling.
Corxor MSSP is an optional operational layer. Customers may run QuickSecure independently, integrate with their internal SOC, engage Corxor as MSSP, or use it via third-party MSSP partners through multi-tenant white-label support. The platform architecture is independent from the service model.
Transparent Per-Endpoint Pricing
Same product at every tier. Capability level and support SLA differ.
- Shadow + Supervised modes
- Basic SOC console view
- Explainable AI scoring
- Collective IoC sync
- 90-day event retention
- Email support (48h SLA)
- AI Security Assistant
- Shadow + Supervised modes
- Built-in SOC console
- Explainable AI scoring
- Collective IoC sync
- 90-day event retention
- Email support (24h SLA)
- JSON export + Webhooks
- AI Incident Explanation
- AI IOC Assessment
- Everything in Business
- Full autonomous mode
- Advanced policy engine
- Confidence-gated containment
- Central SIEM Hub
- 180-day event retention
- Priority support (8h SLA)
- Model version management
- Workspace AI Assistant
- Everything in Advanced
- Enterprise tenant isolation
- Tenant-dedicated ML models
- Multi-tenant SOC dashboard
- Direct SIEM export (Sentinel, Splunk, Syslog)
- Per-tenant rate limiting
- On-premise deployment option
- Custom retention & dedicated support
- AI Governance & Audit
- AI API Access
- Premium Provider Choice
Volume discounts available for 100+ endpoints. First-year pricing guaranteed for annual commitments.
Try the AI Security Engine
Ask a security question to see the same AI engine that powers incident explanation, IOC assessment, and workspace intelligence inside QuickSecure — running live right now.
🟢 Live demo — real AI inference against our self-hosted model with threat intelligence grounding. Click any example or type your own question.
Self-hosted AI inference — no data sent to third parties. Rate-limited public demo.
Unlock full AIYour AI, Your Rules
QuickSecure's AI Security Engine is governed, audited, and tenant-aware. You control the inference path — self-hosted for maximum privacy, or premium providers for enhanced reasoning. No lock-in.
Self-Hosted Default
All AI inference runs on self-hosted infrastructure by default. No data leaves your environment. Zero third-party API calls. Full data sovereignty from day one.
Premium Provider Option
Enterprise customers can optionally enable premium AI providers for enhanced reasoning quality. Provider routing is per-tenant, policy-controlled, and fully audited.
Governed & Auditable
Every AI interaction — regardless of provider — is logged in a tamper-evident audit trail. Model selection, token usage, response quality, and provider fallback events are all recorded.
Privacy-First Path
Self-hosted Qwen/Mistral models via Ollama. No external API calls. Ideal for regulated industries, sovereign environments, and maximum data privacy.
Premium Quality Path
Enterprise opt-in to premium providers (Anthropic Claude, etc.) for complex incident analysis and advanced reasoning. Routed per-tenant with automatic fallback to self-hosted if unavailable.
Questions from CTOs, Architects & SOC Leaders
Get Started
Start with a 14-day free Business trial — up to 10 endpoints, no credit card required.